Remote Access Procedures . Ultimate guide to secure remote access. a remote access policy serves as a guide for remote users connecting to the network.
from www.beyondtrust.com
the term secure remote access covers all security policies, processes, and solutions that protect your. Ultimate guide to secure remote access. Home / security strategy / secure remote access:
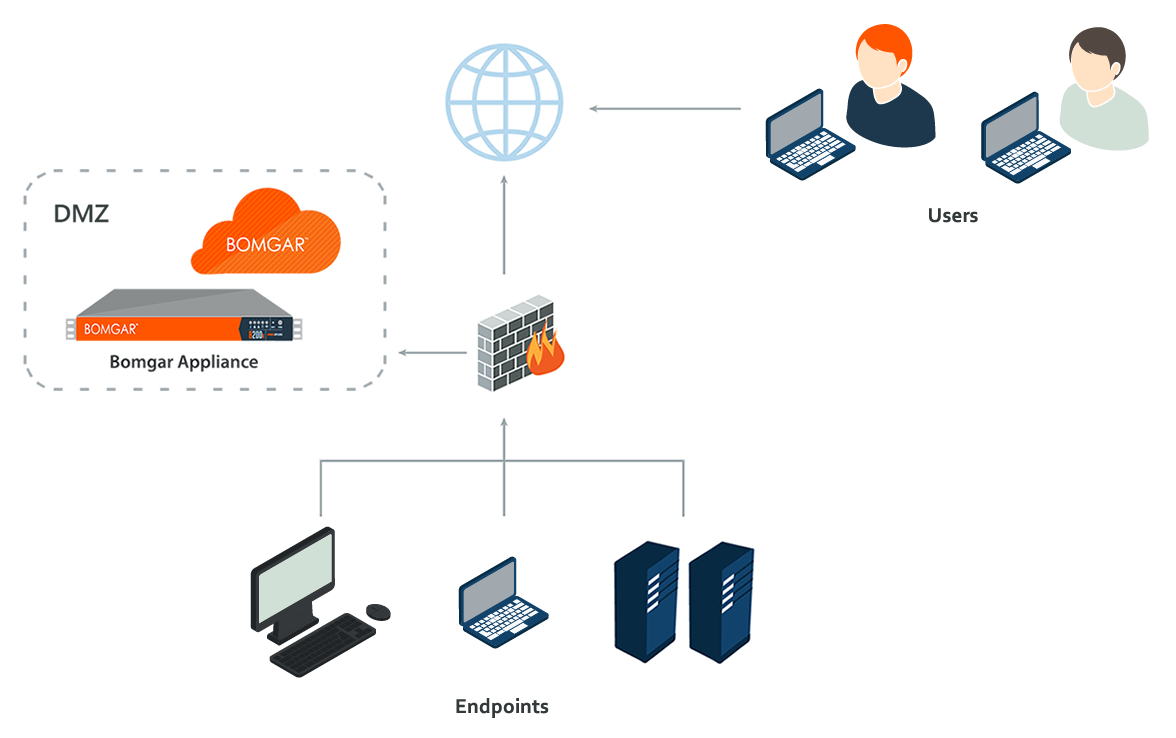
Privileged Remote Access (OnPremises) Security
Remote Access Procedures remote access is any connection made to an organization's internal network and systems from an external source by a device or. remote access is any connection made to an organization's internal network and systems from an external source by a device or. when developing remote access security policies, it leaders should consider defining the following procedures and. a remote access policy serves as a guide for remote users connecting to the network.
From www.bankinfosecurity.co.uk
6 Steps to Secure Remote Access BankInfoSecurity Remote Access Procedures a remote access policy serves as a guide for remote users connecting to the network. the term secure remote access covers all security policies, processes, and solutions that protect your. remote access is any connection made to an organization's internal network and systems from an external source by a device or. What it is & how to. Remote Access Procedures.
From www.scribd.com
Remote Access Procedure Agreement PDF Computer Network Remote Access Procedures Home / security strategy / secure remote access: the term secure remote access covers all security policies, processes, and solutions that protect your. a remote access policy serves as a guide for remote users connecting to the network. Ultimate guide to secure remote access. remote access is any connection made to an organization's internal network and systems. Remote Access Procedures.
From www.thebestsmart.homes
connect to home network remotely How to access a router remotely Remote Access Procedures when developing remote access security policies, it leaders should consider defining the following procedures and. Home / security strategy / secure remote access: What it is & how to establish. a remote access policy serves as a guide for remote users connecting to the network. remote access is any connection made to an organization's internal network and. Remote Access Procedures.
From sujiguna1696.medium.com
Remote Procedure CallRPC. Remote Procedure Call aka RPC is an… by Remote Access Procedures Home / security strategy / secure remote access: the term secure remote access covers all security policies, processes, and solutions that protect your. remote access is any connection made to an organization's internal network and systems from an external source by a device or. What it is & how to establish. Ultimate guide to secure remote access. Remote Access Procedures.
From www.formsbirds.com
Standard Access Control Policy Template Free Download Remote Access Procedures remote access is any connection made to an organization's internal network and systems from an external source by a device or. when developing remote access security policies, it leaders should consider defining the following procedures and. a remote access policy serves as a guide for remote users connecting to the network. the term secure remote access. Remote Access Procedures.
From www.it-procedure-template.com
Remote Access Procedure IT Procedure Template Remote Access Procedures remote access is any connection made to an organization's internal network and systems from an external source by a device or. when developing remote access security policies, it leaders should consider defining the following procedures and. a remote access policy serves as a guide for remote users connecting to the network. Home / security strategy / secure. Remote Access Procedures.
From shop.arlingtonintel.com
Access Control Arlington Security Portal Remote Access Procedures when developing remote access security policies, it leaders should consider defining the following procedures and. What it is & how to establish. the term secure remote access covers all security policies, processes, and solutions that protect your. Home / security strategy / secure remote access: Ultimate guide to secure remote access. Remote Access Procedures.
From www.remote-accesss.com
Most Secure Remote Access Protocol Remote Access Procedures Ultimate guide to secure remote access. Home / security strategy / secure remote access: What it is & how to establish. the term secure remote access covers all security policies, processes, and solutions that protect your. remote access is any connection made to an organization's internal network and systems from an external source by a device or. Remote Access Procedures.
From docs.cyberark.com
Remote access to target machines Remote Access Procedures Home / security strategy / secure remote access: Ultimate guide to secure remote access. remote access is any connection made to an organization's internal network and systems from an external source by a device or. a remote access policy serves as a guide for remote users connecting to the network. What it is & how to establish. Remote Access Procedures.
From www.formsbirds.com
Standard Access Control Policy Template Free Download Remote Access Procedures What it is & how to establish. when developing remote access security policies, it leaders should consider defining the following procedures and. the term secure remote access covers all security policies, processes, and solutions that protect your. Ultimate guide to secure remote access. remote access is any connection made to an organization's internal network and systems from. Remote Access Procedures.
From www.beyondtrust.com
Privileged Remote Access (OnPremises) Security Remote Access Procedures the term secure remote access covers all security policies, processes, and solutions that protect your. What it is & how to establish. a remote access policy serves as a guide for remote users connecting to the network. remote access is any connection made to an organization's internal network and systems from an external source by a device. Remote Access Procedures.
From www.remote-accesss.com
Remote Access Control Policy Template Remote Access Procedures a remote access policy serves as a guide for remote users connecting to the network. What it is & how to establish. Ultimate guide to secure remote access. the term secure remote access covers all security policies, processes, and solutions that protect your. remote access is any connection made to an organization's internal network and systems from. Remote Access Procedures.
From www.remote-accesss.com
How To Establish A Remote Access Policy Remote Access Procedures the term secure remote access covers all security policies, processes, and solutions that protect your. when developing remote access security policies, it leaders should consider defining the following procedures and. Ultimate guide to secure remote access. a remote access policy serves as a guide for remote users connecting to the network. remote access is any connection. Remote Access Procedures.
From papers.govtech.com
The Essential Guide to Securing Remote Access Remote Access Procedures a remote access policy serves as a guide for remote users connecting to the network. when developing remote access security policies, it leaders should consider defining the following procedures and. the term secure remote access covers all security policies, processes, and solutions that protect your. Home / security strategy / secure remote access: What it is &. Remote Access Procedures.
From www.pinterest.co.uk
Remote Procedure Calls (RPC) Protocol Architecture, Types, and Remote Access Procedures remote access is any connection made to an organization's internal network and systems from an external source by a device or. Home / security strategy / secure remote access: a remote access policy serves as a guide for remote users connecting to the network. Ultimate guide to secure remote access. when developing remote access security policies, it. Remote Access Procedures.
From duo.com
The Essential Guide to Securing Remote Access Duo Security Remote Access Procedures What it is & how to establish. when developing remote access security policies, it leaders should consider defining the following procedures and. the term secure remote access covers all security policies, processes, and solutions that protect your. Home / security strategy / secure remote access: Ultimate guide to secure remote access. Remote Access Procedures.
From www.parallels.com
What Is a Remote Access Policy, and Why Is It Important? Remote Access Procedures Home / security strategy / secure remote access: when developing remote access security policies, it leaders should consider defining the following procedures and. What it is & how to establish. the term secure remote access covers all security policies, processes, and solutions that protect your. remote access is any connection made to an organization's internal network and. Remote Access Procedures.
From icma.org
Remote Access Procedure Remote Access Procedures Home / security strategy / secure remote access: the term secure remote access covers all security policies, processes, and solutions that protect your. a remote access policy serves as a guide for remote users connecting to the network. What it is & how to establish. when developing remote access security policies, it leaders should consider defining the. Remote Access Procedures.